New MaaS InfoStealer Malware Campaign Targeting Oil & Gas Sector
As of this moment, there are a high volume of phishing emails that employ several tactics, techniques, and procedures known to assist in bypassing secure email gateways to deliver the malware.
Cofense Intelligence is tracking an advaced campaign that is successfully reaching intended targets in the Oil and Gas industry. The campaign delivers an uncommon, but advanced, Malware-as-a-Service information stealer, the Rhadamanthys Stealer.
This new and advanced phishing campaign employs a recently updated Malware-as-a-Service (MaaS) within days of law enforcement’s takedown of LockBit ransomware group, one of the most active Ransomware-as-a-Service (RaaS).
Based on a report by Cyberint published on January 22nd, the malware family recently received a major update on the black market which could be the reason we’re seeing such an unfamiliar family appear in such an advanced campaign.
As of this moment, there are a high volume of phishing emails that employ several tactics, techniques, and procedures known to assist in bypassing secure email gateways to deliver the malware.
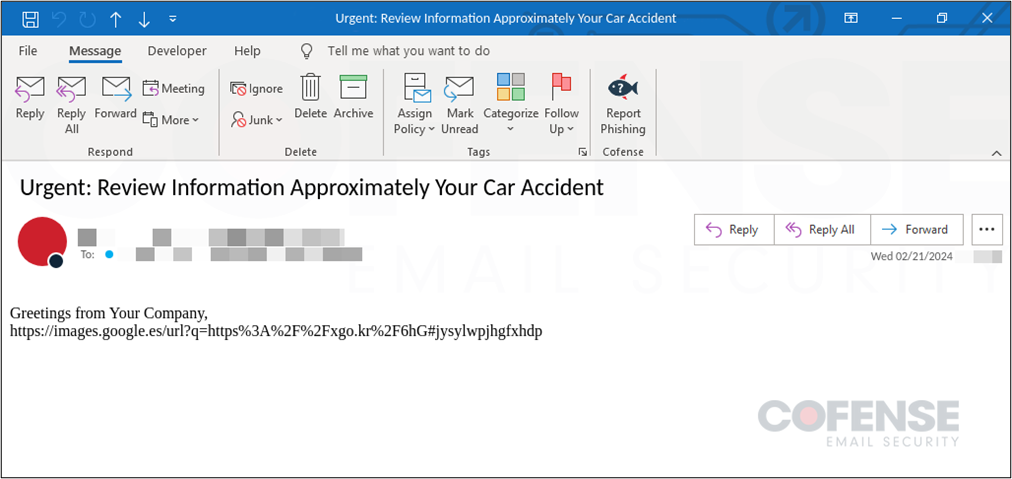
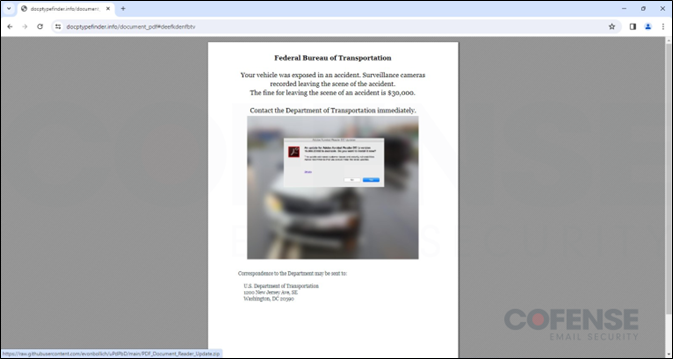
The campaign starts with a phishing email (Above Image) using a vehicle incident report to lure victims into interacting with an embedded link that abuses an open redirect on a legitimate domain, primarily Google Maps or Google Images. Users are then redirected several times before finally reaching an interactive PDF file hosted on a recently registered domain docptypefinder[.]info .
The PDF is a clickable image which reaches out to a GitHub repository and downloads a ZIP archive that contains a Rhadamanthys Stealer executable. Once a victim attempts to interact with the executable, the malware will unpack and start a connection with a command and control (C2) location that collects any stolen credentials, cryptocurrency wallets, or other sensitive information.
Rhadamanthys Stealer is an uncommon but very advanced Malware-as-a-Service that first appeared in 2022 and is written in the C++ programming language. The stealer implements several features to aid in its many stealing capabilities. The primary use for the stealer is for threat actors to steal device information, document files, cryptocurrency wallets, and credentials stored in various applications and browsers. Based on the report by Cyberint the malware recently received a major update to 5.0 giving threat actors who purchase the service a more customizable experience and allowing additional measures to counter security and exploit vulnerabilities. Table 1 at the end of this report shows a sample of the IOCs pulled from this this campaign, and for Cofense customers the full stack can be seen on the Active Threat Report on ThreatHQ.
MORE FROM THE CRUDE LIFE
Please click that ♡ button, share, and subscribe.
Please share the links on social media.
Thank you thank you thank you for your engagement and support.
f you have a news tip, press release, guest suggestion or other content concepts, please email thecontentcreationstudios(AT)gmail(DOT)com
This post was brought to you in part by one of The Crude Life’s fantastic sponsors, please consider supporting their services or learning more about their organization by clicking on the banner below.
Most buyers either walk or drive past a home, real estate, and decide whether or not to enter the property based on the look of the exterior. What many buyers may not realize is that the sellers inside the house may be keener to engage with potential buyers than those standing outside.
The key to selling your house is in making it appealing to as many potential buyers as possible, and having the best real estate agents that can significantly increase your chances of selling your home fast and for top dollar.
We’re in the business of helping people. We just happen to sell real estate.
Follow Hatch Realty on Facebook, LinkedIn, X (Twitter) or their company website.